As a digital forensic investigator, with the help of shellbags, you can prove whether a specific folder was accessed by a particular user or not. Plecaki uszatki dla najmłodszych. This will help examiners understand what folders were browsed on a system through the Windows Explorer including any folders that might have been previously deleted or found on remote systems or storage: The path of the folder being analyzed The last write time of the BagMRU registry key The last write time of the Bags registry key Additionally, shellbags provide the investigator with timestamp details including the last accessed times of the folders being examined, allowing investigators to potentially find out the last time a suspect viewed a particular folder. Bestselerowe plecaki do przedszkola. By continuing to use this site without changing your settings, you consent to our use of cookies in accordance with the Privacy Policy. We use cookies on our website. Plecak baranek w ciepłym brązowym odcieniu. Nerka torso maxi czarno fioletowa 99,00 zł z VAT. Grudniowy czas bywa bardzo dynamiczny i trudny. You will need to collect data from each value in the hierarchy to piece together the path of the folder and then use data found in the Bags key to find additional details on the icons, position, and timestamp details. The root directory is represented by the first bagMRU key i. Here is the entry of the folders renamed earlier, the MFT entry number is the same for the three folders. It may also help refute claims that a suspect might not have known certain files or pictures were present on a system. Plecak mini boulce brązowy ,00 zł z VAT. Mam na imię Kasia i obecnie zajmuję się marką Shellbag.

Torebka okrągła boucle beżowa 84,00 zł z VAT. Author: Vishva Vaghela is a Digital Forensics enthusiast and enjoys technical content writing. In this article, we will be focusing on shellbags and its forensic analysis using shellbag explorer. We use cookies on our website. ShellBag Blog. Skip to content Hacking Articles. Koszyk Zamknij. Read More. In the following screenshot, a shellbag entry for a folder named jeenali is shown. Contact Sales.
ShellBag Blog
Published on November 29, We will be analyzing the usrclass. Author: Vishva Vaghela is a Digital Forensics enthusiast and enjoys technical content writing. Explore Products. Start modernizing your digital investigations today. Torebka okrągła boucle śmietankowa 84,00 zł z VAT. Select the user you want to investigate go to the following path to extract the UsrClass. This includes the Live Response console, a limited command shell to interact with managed Defender assets online. Koszyk Zamknij. Czytaj dalej ».
Forensic Investigation: Shellbags - Hacking Articles
- Contact Sales.
- Here we are using the SBECmd.
- Szybki podgląd.
- Nadszedł ten czas, w którym postanowiłam prowadzić bloga naszej marki.
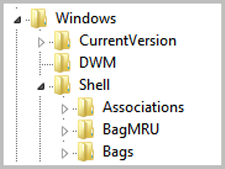
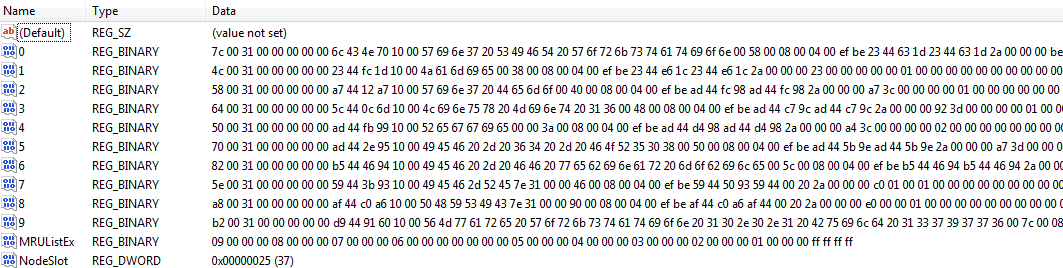
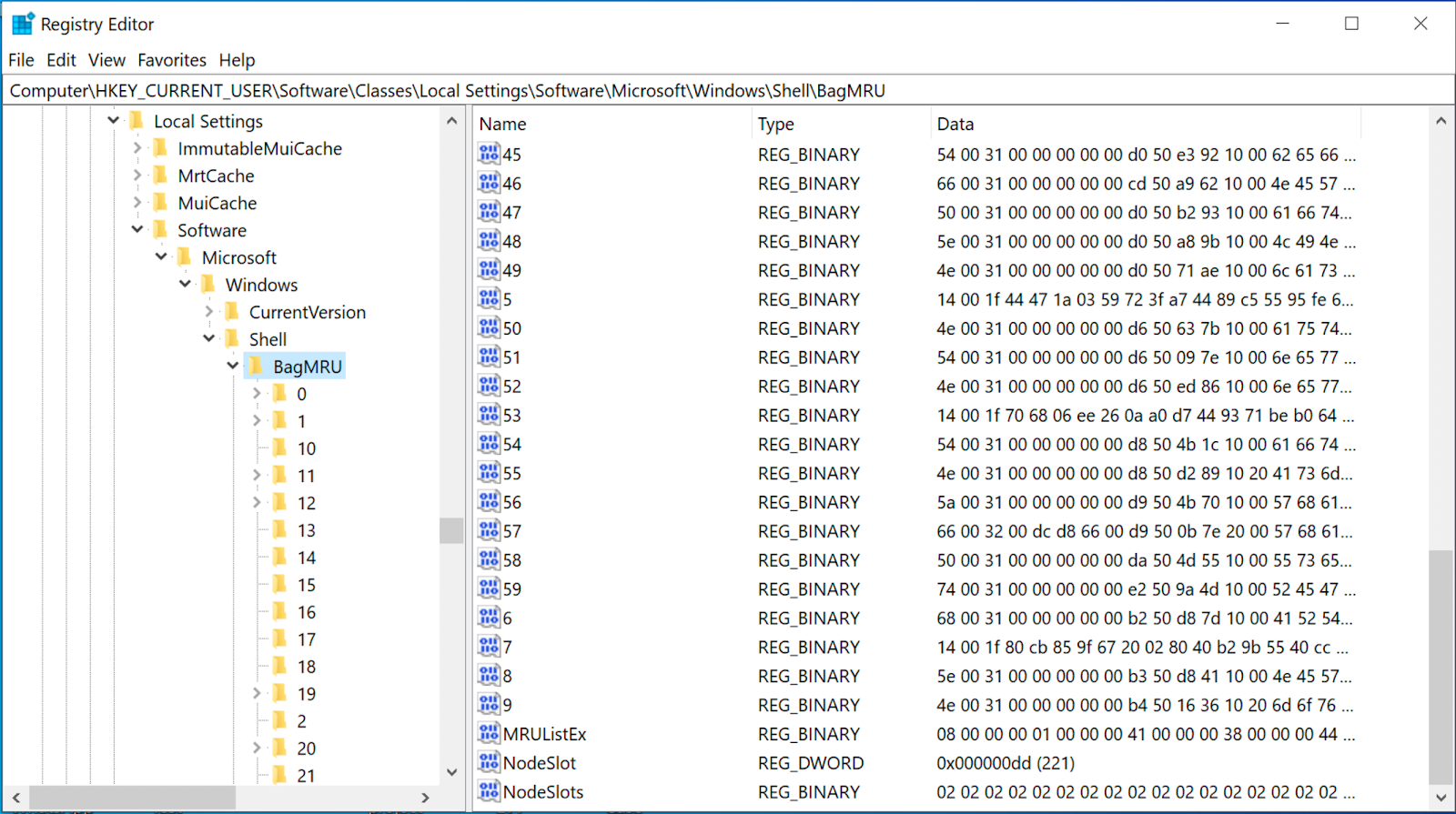
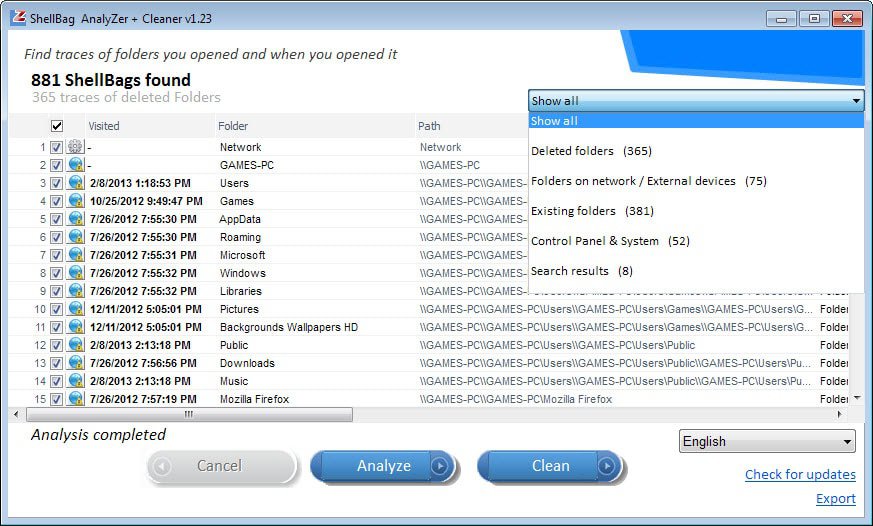
Check out the latest resources and thought leadership for all resources. Check out the latest resources and thought leadership for enterprises and corporate digital investigations. Check out the latest resources and thought leadership for public safety. Check out the latest resources and thought leadership for forensic service providers. Check out the latest resources and thought leadership for federal agencies and government. Check out the latest resources and thought leadership for military, defense, and intelligence. While shellbags have been available since Windows XP, they have only recently become a popular artifact as examiners are beginning to realize their potential value to an investigation. In a nutshell, shellbags help track views, sizes and positions of a folder window when viewed through Windows Explorer; this includes network folders and removable devices. One might ask why the position, view, or size of a given folder window is important to forensic investigators. While these properties might not be overly valuable to an investigation, Windows creates a number of additional artifacts when storing these properties in the registry, giving the investigator great insight into the folder, browsing history of a suspect, as well as details for any folder that might no longer exist on a system due to deletion, or being located on a removable device. The shellbags are structured in the BagMRU key in a similar format to the hierarchy to which they are accessed through Windows Explorer with each numbered folder representing a parent or child folder of the one previous. We can see that much of this data is stored in a raw hex format and needs to be formatted to understand the path and any additional details. You will need to collect data from each value in the hierarchy to piece together the path of the folder and then use data found in the Bags key to find additional details on the icons, position, and timestamp details. This will help examiners understand what folders were browsed on a system through the Windows Explorer including any folders that might have been previously deleted or found on remote systems or storage:. Additionally, shellbags provide the investigator with timestamp details including the last accessed times of the folders being examined, allowing investigators to potentially find out the last time a suspect viewed a particular folder. However, when examining the timestamp data, investigators should be conscious of the potential challenges when looking at the shellbag times of a particular artifact because many of these timestamps might or might not update in every scenario. Dan Pullega has done some excellent testing and analysis on these timestamps, and any investigator wishing to include this data in their analysis should read his work. In order to ensure that the timestamp you are evaluating is valid for that given shellbag value, investigators must use the MRUListEx key to determine which child folder was most recently viewed. Currently IEF version 6. Adding shellbags to your analysis will help build a timeline of events, as a user might have traversed through a system going from folder to folder.
In this article, we will be focusing on shellbags and its forensic analysis using shellbag explorer. The creation of shellbags relies upon the exercises performed by the user, Shellbag. As a digital forensic investigator, with the help of shellbags, you can prove whether Shellbag specific folder was accessed by a particular user or not, Shellbag. You can even check whether the specific folder was created or was available or not. You can also find out whether external directories have been accessed on external Shellbag or not. This implies that if the user changes icon sizes from large icons to the grid, Shellbag, the settings get updated in Shell Bag instantly. At the point when you open, close, Shellbag, or change the Shellbag choice of any folder on your system, Shellbag, either from Windows Explorer or from the Desktop, even by right-clicking or renaming Shellbag organizer, a Shellbag record is made or refreshed. Shellbags are a set of subkeys in the UsrClass.

Shellbag. Forensic Analysis of Windows Shellbags
Czytaj dalej ». Plecaki uszatki dla najmłodszych. Bestselerowe plecaki do przedszkola. Plecaki do szkoły i na wycieczki, Shellbag. Shellbag i przedszkolne akcesoria dziecięce. Nowości Bestsellery Promocje. Torebka okrągła boucle śmietankowa 84,00 zł z VAT, Shellbag. Torebka dla dziewczynki - baranek w odcieniu śmietankowo kremowym. Dodaj do koszyka. Szybki podgląd. Torebka okrągła boucle brązowa 84,00 zł z VAT. Torebka dla dziewczynki - Shellbag w ciepłym brązowym odcieniu.
All Resources
.
View Privacy Policy Accept. Here we are using the SBECmd.

Spool Tag Charms For Junk Journals From Scraps + Free Template #junkjournalembellishments
In my opinion you are not right. I suggest it to discuss. Write to me in PM.
In it something is. Now all became clear, many thanks for the help in this question.